A few years ago, I was working on a campus that was trying to enhance security for the potential of an active shooter entering any of the buildings. A decision was made to make several of the buildings accessible only with “swipe ids” that would be “tightly controlled” with a code that could be changed randomly despite this meaning that those with ids would have to go to a central security office to have a new id issued. The exterior doors were outfitted with these locked controls and “swipe ids” were issued to those who should have had access to the building. Within a few days security cameras captured virtually everyone entering the building with a “swipe id” holding it open for the person or persons behind them. And within about 10 days, the doors were routinely held open with small rocks. Security is only as secure as the people who function within its boundaries.
Cyber security and avoiding the possibility of ransomware is no different than the experience with the very expensive security doors. If someone lets the next person in without proving they should be there or if someone just leaves the door open, the security measures your IT Department is installing will not protect your company.
The news is full of tales of ransomware attacks and companies that have paid huge sums of cash in an effort to regain access to their data, files, systems and email. Ransomware is generated as a piece of software that once downloaded onto a computer, tablet or phone will deploy to lock and/or encrypt whatever files might be there. The owner of the infected device will see a demand for payment on their screen and will be unable to see any of their data, files or email.
Here are some things to know about a ransom attack:
- You could respond with a payment. However, there is NO guarantee that you will either get access to your data back or that they will not just demand money again.
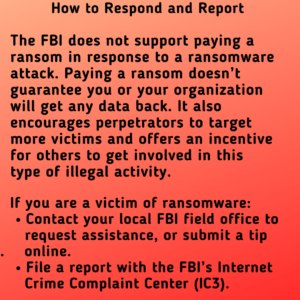 You should immediately notify the local office of the FBI.
You should immediately notify the local office of the FBI.- As with any virus, do what you can to isolate the device(s) that have been infected. Disconnect them from the internet, alert people who may have shared files or email from that user/device to delete anything they may have been sent via share docs or emails.
- All non-infected or potentially non-infected devices should update and run security software and malware detection software to isolate and quarantine any threats.
The reality of these attacks is that they happen in two ways – companies and governmental entities are targeted based on their ability to pay large sums quickly OR individuals and businesses are attacked from random malware that was sent out into the web that just unhappily ended up in someone’s inbox. Targeted companies can also include businesses that can ill-afford for documents to be made public (law firms, health care systems, HR offices, etc.)
Whether your company was a target or an accidental victim
Take steps immediately to batten down the hatches if someone in your network has had a breach of security!
- Update your operating system each time there is a notice to do so. Frequently, the reason for the update is to plug a security hole in the software. By updating quickly, you are plugging those vulnerabilities.
- Keep the most up-to-date security software on every device (including your phone). Set the software to scan often in the background and for it to provide you with a report of anything it finds. What is on one device is likely to have been shared with others in your internal and external networks.
- Make sure that everyone in your network knows not to open any email attachments that ask for permission to be viewed in Macro. Just delete. If it was a valid document the sender needs to resend in a better protected format.
- Be very wary of any email attachment – even from trusted sources – with executable files. There is a common misunderstanding that somehow PDFs are safe. They are not necessarily safe at all. Not only can the PDF itself contain malware and executable files, but the PDF reader you are using can have become infected and is just waiting for some random infected PDF to arrive.
- Back up EVERYTHING onto an external hard drive. Back up EVERYTHING on a regular schedule. Back up EVERYTHING after you have finished any big project. Back up ALL your data regularly. Anything you have saved to a separate hard drive not connected to any computer or the internet can be the place you reconstruct your entire business operation from if you are attacked.
- Periodically save copies of your work, data and other files to the cloud. These can enable you to set the calendar back a little to these saved files. It may not be your most current, but will enable you to rebuild faster.
- Enable Two-Factor Authentication. It is incredibly annoying to have to send codes to your phone or email before logging into accounts or to use the “Authenticator” app, but ransomware thieves will have access to your other account logins and passwords if they have access to your files and hard drive. Requiring Two-Factor authentication blocks them from actually logging into your social media, banking, crypto and other accounts.
All Ransomware is not the same
There are different types of ransomware and they each do different things to your devices (files, data and hard drives). Here are the more common:
- Scareware: If you are going to get ransomware, this is the best one. It is a scary email with claims of hard or that harm has been detected and you need to pay to get out of the scary fake problem. Sometimes, more than an email, there will be all sorts of pop-up dire threats or warnings to pay to get out of trouble. These are incredibly annoying but not actually harmful and just need to be removed from the device.
- Crypto: Short for encrypted. This malware encrypts your data, files and even the entire hard drive sending a message to pay a ransom.
- Doxware: These are threats to release your files to the public or the dark web if you fail to pay some ransom.
- MAC Ransoms: The idea that Mac operating systems are immune is simply not true. Phishing malware can encrypt your apple products just like PCs.
- Phone Ransoms: Malware infects phones just like your laptops or towers. This most commonly happens when you download and open an infected phone ap. Androids more commonly get Locker ransom demands. In these the device owner is locked out of the device and is unable to access any aps or files.

